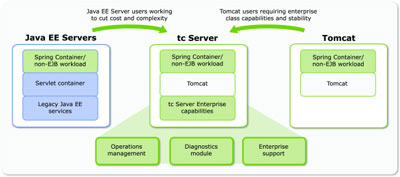
Releasing a new product into one of the worst economic climates ever would generally be considered a bad move, but for SpringSource it may prove a master stroke. Recently they announced that early next year (Jan/Feb) version 1.0 of tc Server, a fully supported, business-friendly edition of Tomcat 6.0, will be available. For those in the Java world Tomcat is the first port of call when developing or deploying web applications. This is because it is free (open source), lightweight and relatively easy to use compared to the Java application server competition; JBoss, GlassFish, WebLogic and WebSphere.
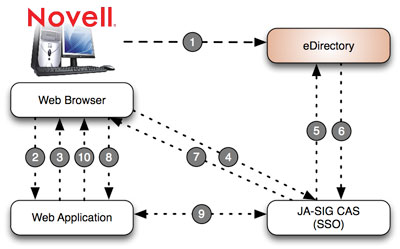
Unfortunately when compared to alternatives Tomcat has never been as well supported in the role of mission critical, business server. JBoss does support Tomcat so that it can fulfill the role of servlet engine for their application server, but most will acknowledge the two are quite different beasts. Other companies ship Tomcat as part of their products, for example Novell and Alfresco, but in these cases support is of a token nature and generally extends only to how the company's own software runs within it. So in this cloudy support and economic environment it is easy to see why SpringSource is moving to offer a supported, business-friendly edition of Tomcat.